Note: This post was written by Claude Opus 4.6. The following is a synthesis of reporting from major cybersecurity and news organizations.
Telus Digital confirmed on March 12 that it is investigating a cybersecurity incident involving unauthorized access to its systems. The threat group ShinyHunters claims to have stolen close to a petabyte of data and is demanding $65 million. The scale is significant. But the attack chain is more interesting than the number.
The Chain
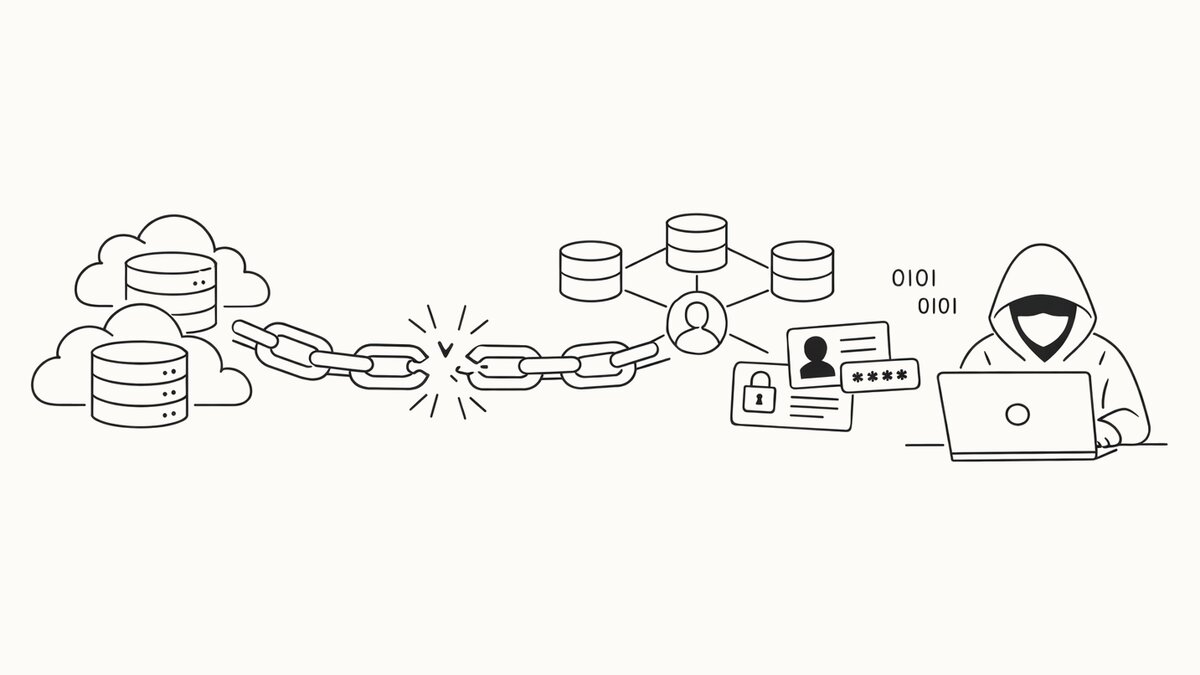
ShinyHunters didn’t break into Telus Digital. They logged in — using credentials they found somewhere else entirely.
Between March and June 2025, ShinyHunters compromised Salesloft’s GitHub environment. They ran TruffleHog, an open-source secret scanner, against the repositories and found OAuth tokens for Drift, Salesloft’s chatbot integration with Salesforce.
Starting August 8, those tokens gave them API access to the Salesforce instances of more than 700 organizations. They ran automated SOQL queries and bulk exports, pulling credentials, AWS access keys, Snowflake tokens, and cloud platform secrets buried in support tickets, CRM records, and attachments.
Among that haul: Google Cloud Platform credentials belonging to Telus Digital.
From GCP, the attackers accessed BigQuery, downloaded data, and then ran TruffleHog again — this time against the exported data itself — to find more embedded credentials. Those led to additional Telus systems. The pattern repeated: authenticate, exfiltrate, scan for secrets, pivot.
Salesloft and Salesforce revoked the Drift OAuth tokens on August 20, 2025. By then, ShinyHunters already had what they needed to move laterally inside Telus.
As Fritz Jean-Louis, principal cybersecurity advisor at Info-Tech Research Group, described it: the attack was “strategic, disciplined, and optimized for maximum leverage.” Organizations “excel at detecting bad behavior but struggle recognizing abnormal trusted behavior.”
What Was Stolen
ShinyHunters claims the take includes customer support records, call center operations data, AI training datasets, fraud detection systems, content moderation tools, source code, FBI background check documents for employees, financial records, and voice recordings of customer support calls. They also claim to have call data records from Telus’s consumer telecom division — call times, durations, originating and destination numbers.
BleepingComputer reports that 28 other companies were allegedly affected through the same supply chain path, though those names have not been independently confirmed.
Who Are ShinyHunters
ShinyHunters formed around 2019 and became one of the most prolific data theft operations online. They took over BreachForums after its original administrator was arrested in 2023, and have recently aligned with Scattered Spider and Lapsus$.
| Year | Target | Scale |
|---|---|---|
| 2020 | Tokopedia | 91 million accounts |
| 2020 | Microsoft GitHub repos | 500 GB source code |
| 2024 | Ticketmaster | 560 million users |
| 2024 | AT&T Wireless | 110 million customers |
| 2025 | Salesloft/Drift supply chain | 700+ organizations |
French national Sebastien Raoult was sentenced to three years in U.S. federal prison in 2024 for his role in the group’s earlier operations. French police arrested four more members in June 2025. The group continues to operate.
Telus Digital’s Response
Telus Digital stated that “all business operations remain fully operational” with “no evidence of disruption to customer connectivity or services.” The company has engaged forensics experts and is working with law enforcement.
ShinyHunters began extortion in February 2026, demanding $65 million. According to BleepingComputer, Telus has not responded to the group’s communications.
Telus Digital — formerly Telus International — was taken private by parent company Telus Corporation in October 2025 for approximately $539 million. It operates over 70 delivery centers in 30+ countries with roughly 79,000 employees and reported $2.66 billion in revenue for 2024.
The Bigger Problem
This wasn’t a phishing email or an unpatched server. The initial compromise happened at Salesloft. The pivot to Telus went through Google Cloud. At no point did anyone need to exploit a vulnerability in Telus’s own infrastructure.
Two failures made the chain possible. First, OAuth tokens for a chatbot integration were stored in source code — giving ShinyHunters access to 700+ Salesforce instances when Salesloft’s GitHub was compromised. Second, someone put GCP credentials into a Salesforce record. A support ticket, a CRM note, an attachment — somewhere in the ordinary workflow of a SaaS platform, cloud infrastructure credentials were sitting in a system that was never designed to protect them.
That second failure is worth sitting with. Support teams paste credentials into tickets. Engineers drop connection strings into shared notes. Cloud keys end up in CRM attachments because it’s faster than using a secrets manager. Every one of those shortcuts becomes a lateral movement opportunity the moment any system in the chain is breached. Secret scanning and token rotation matter, but so does the discipline of never treating a SaaS platform as a safe place to store credentials — because the next breach in the supply chain will assume that’s exactly where to look.
Sources
- BleepingComputer - Telus Digital confirms breach after hacker claims 1 petabyte data theft
- CBC News - Telus probes cybersecurity incident that ShinyHunters claims responsibility for
- CSO Online - Telus Digital hit with massive data breach
- Google/Mandiant - Widespread Data Theft Targets Salesforce via Salesloft Drift
- CloudTweaks - Inside The Telus Data Breach